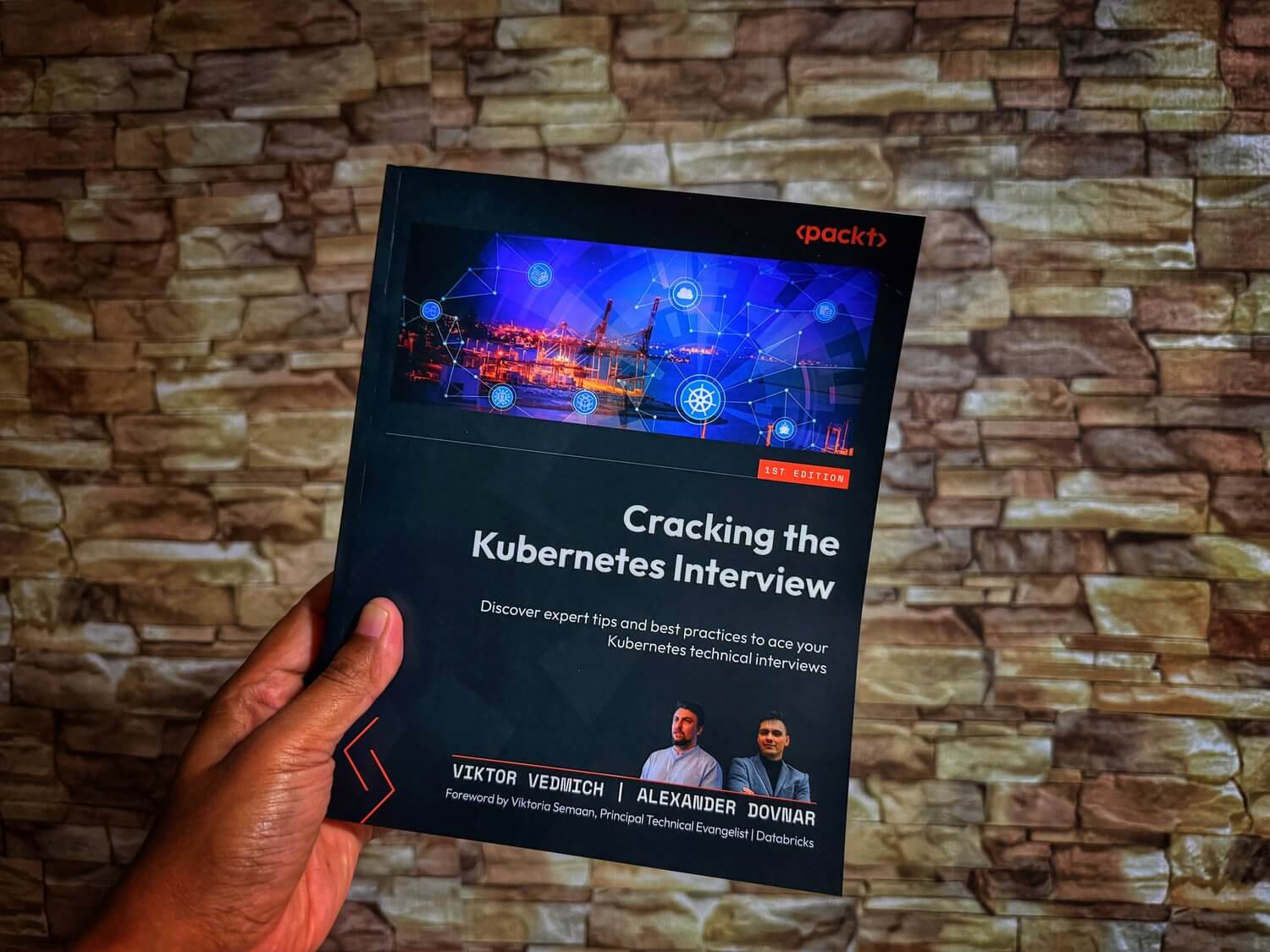
How to Configure SSH-Based Signed Commits in GitHub for the 'Verified' Badge
-
 Gineesh Madapparambath
Gineesh Madapparambath
- Git, Security, Dev ops
- March 5, 2026
In the world of open-source and collaborative coding, identity matters. By default, Git allows anyone to configure their local environment with your name and email. Commit signing is the solution—a digital “wax seal” that proves you are the actual author of the code.
While GPG was the traditional standard, Git 2.34+ allows you to use your existing SSH keys for signing, making the process much simpler.
What is a Signed Commit?
A signed commit uses a cryptographic key to sign the data in your commit. When you push to GitHub, it validates that signature against the public key on your profile. If they match, you get the coveted green Verified badge.
Why Should You Care?
- Security: Prevents “impersonation” where someone else commits code using your identity.
- Trust: In professional environments, it ensures the integrity of the codebase.
- Aesthetics: Let’s be honest—that green badge looks great in your contribution history and PRs.
Step 1: Identify Your SSH Key
First, find the public key you are already using for GitHub. In your terminal, list your keys:
ls -al ~/.ssh
Identify the key you want to use (e.g., id_rsa.pub). Copy the content of your public key to your clipboard:
cat ~/.ssh/id_rsa.pub
Step 2: Add the “Signing Key” to GitHub
This is the most critical step. Even if you already use this key for pushing code (Authentication), GitHub requires you to add it specifically as a Signing Key.
- Log in to GitHub and go to Settings > SSH and GPG keys.
- Click New SSH key.
- Crucial: Change the Key type dropdown from “Authentication Key” to Signing Key.
- Paste your key and save.
Step 3: Configure Your Local Git
Now, tell your local Git instance to sign every commit using that SSH key. Run these commands:
# 1. Set the signing format to SSH
git config --global gpg.format ssh
# 2. Point to your public key file
git config --global user.signingkey ~/.ssh/id_rsa.pub
# 3. Enable automatic signing for every commit
git config --global commit.gpgsign true
Step 4: Verification
Now, make a test commit and push it to your repository.
git commit -m "Test signed commit"
git push origin main
Visit your repository on GitHub.com. You should now see the green Verified badge next to your commit.
Troubleshooting: Why is it “Unverified”?
If you see an orange “Unverified” badge or no badge at all, check these three things:
- Email Match: Your
git config user.emailmust match a verified email on your GitHub account. - Key Type: Ensure you added the key as a Signing Key on GitHub, not just an Authentication Key.
- Git Version: Ensure you are running Git 2.34 or higher (
git --version).
Conclusion
Setting up signed commits takes less than five minutes but significantly levels up your Git security posture. It’s a small badge that makes a big statement about your attention to detail and security best practices.
Happy (Secure) Coding!
Gineesh Madapparambath
Gineesh Madapparambath is the founder of techbeatly. He is the co-author of The Kubernetes Bible, Second Edition and the author of Ansible for Real Life Automation. He has worked as a Systems Engineer, Automation Specialist, and content author. His primary focus is on Ansible Automation, Containerisation (OpenShift & Kubernetes), and Infrastructure as Code (Terraform). (Read more: iamgini.com)
Note
Disclaimer: The views expressed and the content shared in all published articles on this website are solely those of the respective authors, and they do not necessarily reflect the views of the author’s employer or the techbeatly platform. We strive to ensure the accuracy and validity of the content published on our website. However, we cannot guarantee the absolute correctness or completeness of the information provided. It is the responsibility of the readers and users of this website to verify the accuracy and appropriateness of any information or opinions expressed within the articles. If you come across any content that you believe to be incorrect or invalid, please contact us immediately so that we can address the issue promptly.